What is a virtual data room? The data room solution allows you to securely protect information and not worry about the fact that it may be sent to third parties, thanks to a special technology of binding each specific letter and/or attachment to the user device of the recipient.
What Should You Know About the Virtual Data Room?
Consumer policy must take into account the vulnerabilities of different consumer groups that need to be targeted by protection and awareness. In this way, they can provide the benefits of new technologies that are common to society as a whole. For example, some consumer groups, such as the elderly, may be more at risk of online fraud. Even more, data protection and privacy issues can be more sensitive when it comes to IoT products used by children, as they are less aware of the risks.
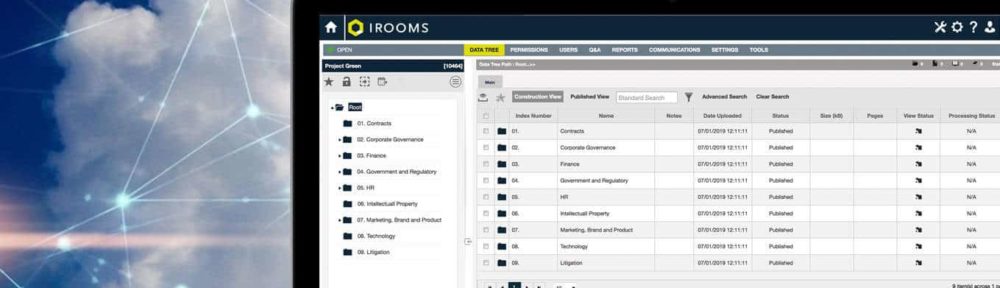
Access to the data room storage can be arranged within a data center or terrestrial infrastructure, and you can quickly adjust the amount it needs. Employees of the data room company will upload files to a shared drive, by default the files and folders on that drive are public. For personal files, each employee is provided with a personal disk. File access is customizable: Allow selected colleagues to read, view, or edit.
Among the main characteristics of the virtual data room are:
- One-button attachment protection for email.
- The high degree of protection against burglary.
- Compatible with all popular corporate email programs.
- Attachment usage statistics.
- Possibility of completion of the system under the requirements of the customer.
Data files in the virtual data rooms are usually grouped into filegroups or tablespaces. A tablespace or filegroup is a logical grouping of multiple data files that store data with similar characteristics. For example, the system tablespace stores metadata, a user-data tablespace for storing user-created tables, an index tablespace for storing all indexes, and a temporary tablespace for temporary sorts, grouping, etc.
Successful M&A Activity with the Virtual Data Room
Small and medium-sized enterprises making the M&A activity with the virtual data room are the most common targets for policies aimed at increasing digital skills, awareness and acceptance of technologies, as well as information campaigns on digital security and privacy technologies. It is also possible that delays and additional efforts due to deviations from quality requirements, the inability of people to perform their duties, external reasons or changes in the content of the project, etc. Deviations in duration or cost indicate the need to control one or more project management functions.
M&A activity with the data room system performance requires a holistic approach. All factors must be checked to ensure that each is operating at its optimum level and has sufficient resources to minimize the occurrence of bottlenecks. The database architecture is an important factor in determining the efficiency of the database system.
The main goal of providing a comprehensive data security system to protect the enterprise for M&A activity is:
- Create favorable conditions for normal functioning in an unstable environment.
- Ensure your own safety.
- Opportunity to legally protect their own interests from illegal actions of competitors.
- Ensure the safety of life and health of the employee.
- Prevent the possibility of material and financial theft, distortion, disclosure, and leakage of confidential information, waste, production violations, destruction of property and ensure normal production activities.